Enzoic combines the most comprehensive, complete, and actionable threat research data with automated remediation to help you strengthen your cybersecurity posture.
Try Now
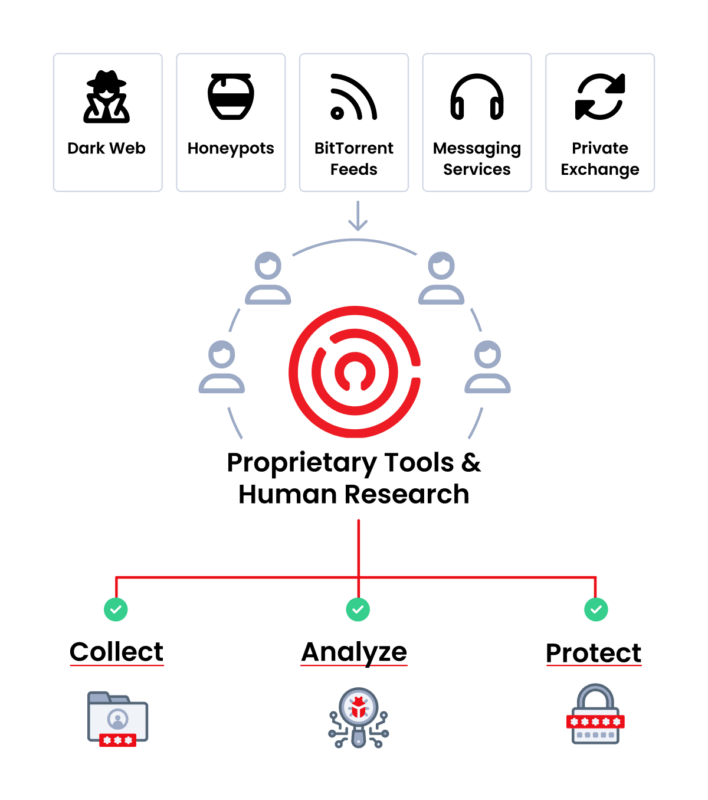
How do we provide our clients with the most current and complete protection?
Our trained analysts scour the public Internet, Dark Web and work with private sources. This human intel is combined with our proprietary tools that automatically intercept and download data 24/7, normalizing and indexing new exposures.
Our credentials and passwords database is updated continuously as new data is obtained, and cleaned from invalid data, duplicated credential records, and data that would lead to unnecessary alert fatigue. This is what makes Enzoic’s threat intel the most current, complete, and actionable.
Learn more1,112
80%
72%
10.07
26,000
PRODUCTS AND SOLUTIONS
Enzoic uses our threat intelligence database to power products and solutions that provide in-depth protection with no added user friction. What is your biggest challenge?
Blog
Defending Against the Infostealer Threat: Learn how to stymie the flow of attacks and protect your personal information with Enzoic's real-time alerts for compromised data.
Blog
Better Active Directory security with Enzoic 3.6: Real-time password feedback. CrowdStrike SIEM integration. Clearer credential risk insights.
Blog
The Verizon 2025 DBIR continues to be at the forefront of cybersecurity research analysis, and Enzoic is proud to be an official contributor.
Make detecting and eliminating compromised passwords in Active Directory easy with a simple plug-in. Start protecting for free.
Try Now