Helping organizations prevent account takeover by detecting compromised credentials, exposed personally identifiable information (PII), and vulnerable payment card data.
![]()

Enzoic is a leading provider of compromised credential detection and account takeover (ATO) prevention solutions. As infostealer malware and credential-based attacks continue to surge, Enzoic helps organizations protect workforce identities, customer accounts, and payment ecosystems by monitoring for credentials and PII exposed through data breaches, credential theft, and dark web sources.
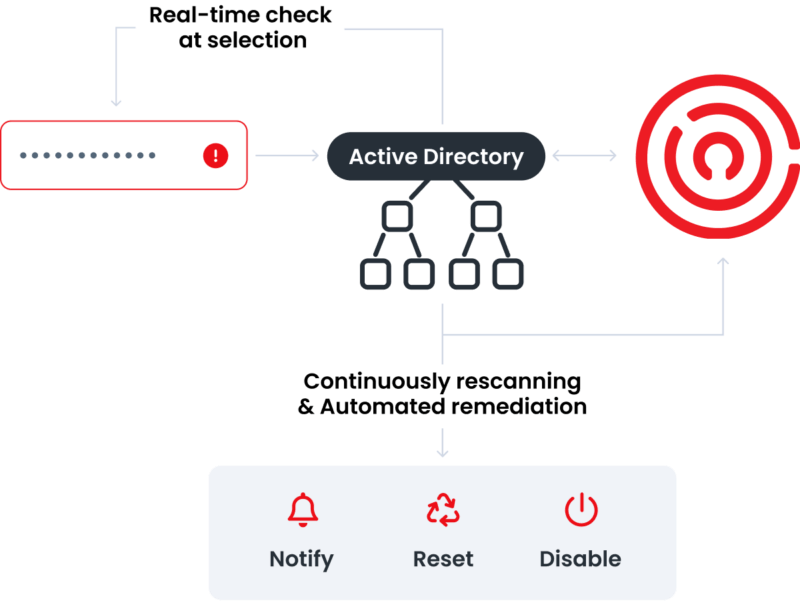
Through our APIs and Active Directory password protection solutions, Enzoic helps organizations reduce risk without adding unnecessary friction to authentication or login experiences.
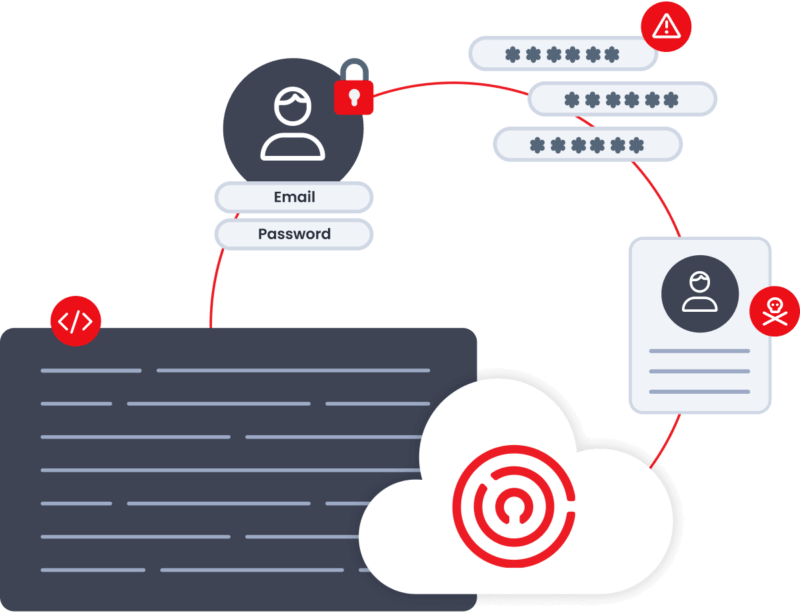
Attackers are becoming more sophisticated every year—and increasingly, they log in instead of breaking in. Traditional authentication confirms whether credentials are correct, but not whether they’ve already been exposed.
Enzoic helps organizations identify and block stolen credentials in real time through seamless integration into Active Directory and authentication workflows. Our easy-to-deploy solutions strengthen security controls, reduce credential-based risk, and stop attacks before they succeed.
Leadership with deep experience in cybersecurity, identity protection, and enterprise software
The Enzoic leadership team blends deep software expertise with innovation across cybersecurity, identity protection, and enterprise technology. From Fortune 500 companies to high-growth security organizations, our leaders understand the complexity of protecting identities at scale.
Our products are built to make customers more secure without creating additional burden for users or security teams.
Headquartered in Boulder, Colorado, Enzoic has helped organizations worldwide prevent credential-based attacks and strengthen identity security through continuous credential intelligence since 2016.

30+ years in technology, software, and cybersecurity; nearly 15 years as CEO. Former organizations include ID Watchdog, Symantec, Webroot, PC Tools, Micromedex, Baxter, and Raindance. Led ID Watchdog through its acquisition by Equifax.

30+ years in technology, software, and cybersecurity; nearly 15 years as CEO. Former organizations include ID Watchdog, Symantec, Webroot, PC Tools, Micromedex, Baxter, and Raindance. Led ID Watchdog through its acquisition by Equifax.

30+ years in technology leadership across SaaS, FinTech, IoT, and cybersecurity. Former roles include CTO, technology leadership, and advisory positions across enterprise software and high-growth technology organizations.

30+ years in technology leadership across SaaS, FinTech, IoT, and cybersecurity. Former roles include CTO, technology leadership, and advisory positions across enterprise software and high-growth technology organizations.

Leadership across revenue growth, enterprise sales, and strategic partnerships in cybersecurity and identity security. Former roles include enterprise sales, partner development, and growth leadership across security-focused organizations.

Leadership across revenue growth, enterprise sales, and strategic partnerships in cybersecurity and identity security. Former roles include enterprise sales, partner development, and growth leadership across security-focused organizations.
WHAT ENZOIC OFFERS
Enzoic’s Active Directory, APIs, breach monitoring, and credential intelligence solutions are powered by continuously updated threat intelligence designed to stop credential-based attacks before they succeed. We provide:
THREAT INTELLIGENCE
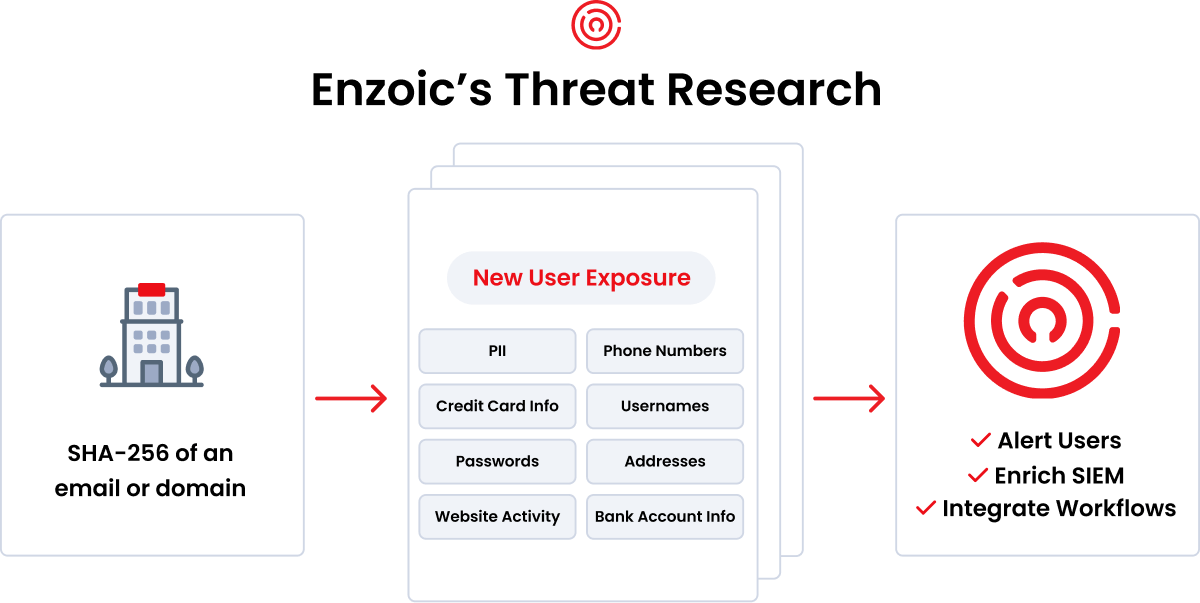
Credential exposure moves fast. Enzoic’s custom-built ingestion systems operate 24/7 to collect, process, validate, and deploy compromised credential intelligence with speed and accuracy.
Our automated deep and dark web collection continuously identifies new exposed credentials, while our threat research team expands visibility across breach sources, infostealer malware, dark web marketplaces, and evolving attacker infrastructure.
SECURITY
At its core, Enzoic is a large-scale cloud platform powered by continuously updated credential intelligence that helps organizations identify and block compromised credentials before attackers can use them.
Designed for security-sensitive environments, Enzoic supports workforce identity protection, customer authentication, and payment-card exposure monitoring without storing submitted credentials. No clear text passwords or credential hash data leave your environment.
Learn more about our securityJoin the thousands of companies using Enzoic products and solutions