A dark web monitoring solution that continuously screens for exposed data to protect user identities and digital assets.
HOW IT WORKS
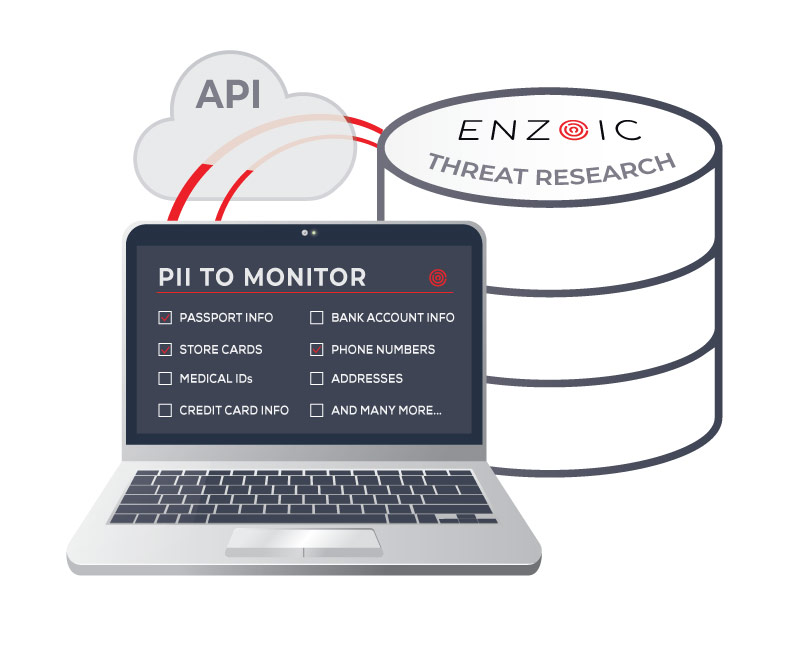
Enzoic’s Identity Breach and PII Monitoring helps organizations continuously monitor for the exposure of personally identifiable information (PII), reducing the risk of identity theft and data abuse for financial gain, fraud, or account takeover. Our straightforward monitoring service allows organizations to safeguard their users without building complex queries and parsing data.
Download the Identity Breach Monitoring BriefHOW IT CAN HELP ME
Be instantly notified of compromised PII, including credit cards, Social Security Numbers, cryptocurrency wallets, and much more.
Enzoic’s extensive research capabilities provide comprehensive visibility into Dark Web data to protect PII and your users.
Continuously track the PII that’s relevant for your workflows by subscribing to other data elements outside Enzoic’s default PII list.
Enzoic gathers and provides data in real-time, without the delays and resources required for you to periodically query an unstructured database.
Prompt notification allows for swift remediation, enabling users to safeguard their accounts and data from identity theft, fraud, and unauthorized access.
FEATURES
Featuring a user-friendly API that seamlessly integrates and expands with your projects.
Real-time alerting of new exposure, plus optional querying of past breach data where identities were previously compromised.
Enzoic’s dedicated research team and proprietary tools, provide immediate and actionable alerting.

The Identity Breach Monitoring API allows you to register complete identities with Enzoic, so that you can be notified about future breaches that involve them.
Explore quick-start guides, code snippets, and a comprehensive resource library to integrate into your workflows.
Read DocsDark web monitoring is the process of scanning dark web forums, underground marketplaces, breach databases, paste sites, criminal forums, infostealer logs, and other exposed data sources for stolen or leaked personal information. Organizations use dark web monitoring to identify compromised credentials, exposed PII, and identity-related risks before they lead to identity theft, fraud, or account takeover. Enzoic’s Identity Breach and PII Monitoring solution continuously monitors for exposed identity data and helps organizations respond quickly to new threats.
Enzoic can monitor a wide range of personally identifiable information (PII), including email addresses, phone numbers, Social Security Numbers, credit card numbers, bank account information, cryptocurrency wallets, login identifiers, and other sensitive identity attributes. Organizations can also customize monitoring based on the specific data elements most relevant to their workflows and users.
Yes. Enzoic provides real-time monitoring for newly discovered exposures and also offers optional access to historical breach data showing where identities, credentials, or personal information may have been previously exposed. This helps organizations better understand past exposure risks while continuing to monitor for new threats.
If your identity information is exposed on the dark web, cybercriminals may attempt to use it for identity theft, fraud, phishing scams, unauthorized account access, or account takeover attacks. Exposed information can also be combined with other stolen data to target financial accounts or online services. Enzoic helps organizations identify these exposures quickly so they can notify users and take action before additional damage occurs.
Protecting your identity starts with using strong, unique passwords for every account, enabling multi-factor authentication (MFA), monitoring for breach exposure, and responding quickly to alerts about compromised information. Enzoic helps organizations continuously monitor for exposed identities and PII so users can take action early, such as changing passwords, securing accounts, or increasing authentication protections.
Stolen personal information can be used for identity theft, financial fraud, phishing attacks, synthetic identity fraud, unauthorized purchases, or account takeover attacks. In some cases, attackers combine exposed credentials and PII from multiple breaches to impersonate victims, access financial accounts, or bypass security checks. Continuous monitoring and rapid exposure alerts can help reduce the risk of these attacks succeeding.
Blog
Sensitive personal information is highly sought after by cybercriminals. As identity theft incidents continue to rise, organizations need effective solutions to protect PII.
Blog
What is identity theft, and what’s happening to increase the impact so dramatically? Read what enterprises can do to make positive change.
Blog
Digital identities are the keys to our online worlds. Recent analyses uncover why organizations must take a strong approach to security.
Talk to us about integrating Dark Web Monitoring into your applications or workflows.
Contact Us