Card issuers can proactively track credit and debit cards by BIN for Dark Web exposure, enabling faster action to prevent compromised card fraud.
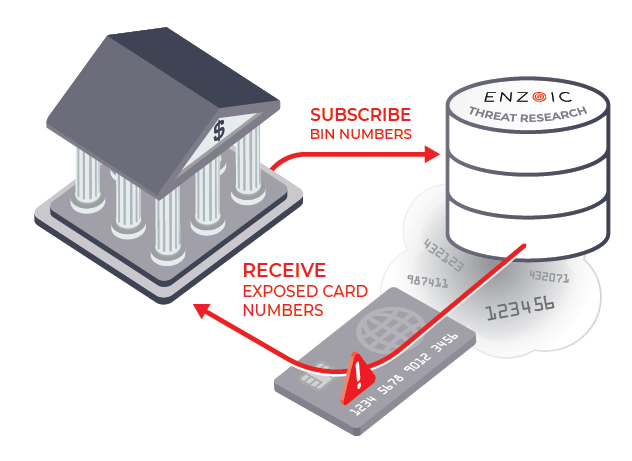
HOW IT WORKS
Enzoic’s Credit Card and BIN Monitoring enables card issuers to subscribe their bank identification number (BIN), also known as the issuer identification number (IIN), to receive timely alerts when credit, debit, or other payment card data appears on the Dark Web. When exposure is detected, an immediate alert containing the full compromised card number is sent, allowing issuers to take proactive action before fraud occurs. Designed for flexibility, these alerts can be integrated with SIEM platforms, card management systems, fraud operations tools, or other existing workflows.
Download the Credit Card and BIN BriefHOW IT CAN HELP ME
A single compromised credit or debit card costs issuers an average of $2,500, making early detection essential. Early visibility also helps prevent card-not-present (CNP) fraud, one of the most common ways exposed card numbers are exploited. By monitoring credit and debit card BIN numbers for Dark Web exposure, Enzoic’s BIN monitoring helps issuers reduce financial losses, protect revenue, and minimize customer disruption. This early insight strengthens fraud defenses, prevents operational strain on support teams, and enhances cardholder trust.
FEATURES
Our threat research team continuously curates one of the most comprehensive and up-to-date collections of BIN and payment card exposure data from across the Dark Web.
Machine learning models analyze patterns across Dark Web sources, mapping relationships between users, communities, and data to surface compromised cards with greater accuracy and coverage.
Issuers can take immediate action when breaches containing credit or debit card numbers associated with their BINs are discovered, enabling faster response and reducing the risk of downstream fraud.
WHY ENZOIC
While VISA CAMS alerts and Mastercard ADC alerts typically notify issuers after potential fraud has occurred, Enzoic’s BIN monitoring provides real-time Dark Web exposure alerts the moment compromised card data is detected. This gives issuers an earlier signal so fraud teams can act quickly before downstream losses, chargebacks, or customer disruption escalate. It also strengthens existing payment real-time fraud monitoring programs by providing upstream exposure insights.
Enzoic’s alerts are highly customizable and integrate easily via an API, working alongside issuer systems such as Fiserv to ensure the right teams receive actionable intelligence as soon as exposure appears online, initiating automatic remediation.

No need for data queries or manual pulls. Enzoic seamlessly integrates into existing workflows—including SIEM, card management, and fraud operations tools—making implementation fast, low-overhead, and simple for issuers. You can also access a dedicated dashboard that gives issuers a clear, real-time view of compromised card activity.
Explore quick-start guides, API documentation, and a full resource library:
Read Technical DocsBlake Rodemeyer, Director of Information Services
“We’ve entrusted Enzoic with the crucial task of monitoring the Dark Web for any potential exposure of our card numbers in 3rd party data breaches. It’s reassuring to know that we have a proactive system in place that keeps a vigilant eye on potential exposures, ensuring our members are protected from fraud.”
A BIN (also referred to as an IIN or issue identification number) is assigned to a bank for its own credit or debit card issuance and is usually the first four, six, or eight digits of a card number. The ISO Register of BINs for US banks and credit unions is managed by the American Bankers Association.
One of the primary ways credit card information can be leaked is through data breaches. Data breaches occur when unauthorized individuals gain access to secure databases and extract sensitive information, which can include credit card numbers, expiration dates, and CVV codes, among other personal data. These breaches can occur in all sectors including retail, finance, healthcare, and online services. Once the data is compromised, it can be sold, traded, or used for fraudulent activities, often appearing on the Dark Web subsequently.
A BIN attack is when a cybercriminal uses brute-force computing to guess and uses an accurate combination of a debit or credit card number, Card Verification Value (CVV), and expiry date. Once this has been completed and the fraudster acquires the right information, they use the card to commit fraudulent transactions in the cardholder’s name or sell the exposed cards on the Dark Web. A botnet can quickly test hundreds or thousands of combinations.
The exposure of card information through data breaches and BIN attacks poses severe challenges for issuers. Financial institutions bear the brunt of the consequences, facing both financial and operational repercussions. They are responsible for absorbing the cost of fraudulent charges resulting from BIN attacks, which includes not only the financial losses but also the associated operational and business costs. The repercussions extend to dealing with chargebacks, managing increased call center activity, and undertaking the process of card re-issuance.
Moreover, these breaches and attacks inflict damage on an institution’s reputation, leading to a loss of trust among cardholders and a resulting long-term impact on customer relationships. Additionally, financial institutions experience losses in interchange revenues, including less favorable interchange rates in a response to high amounts of fraud.
Once a compromised card is identified, financial institutions can take several immediate actions including blocking suspicious transactions, increasing scrutiny on the affected accounts, notifying the customer, reissuing a new card, and updating their fraud detection models. Moreover, the institutions can work with law enforcement agencies to address the compromise and investigate its origins.
Absolutely. Enzoic designed this service for flexibility and can seamlessly integrate into new or existing workflows, including SIEMs, card management, customer communication management, and even proprietary systems. This ensures minimal resource demands and allows for easy implementation within your existing security infrastructure.
Enzoic’s real-time alerting system notifies financial institutions the moment breaches containing debit and credit card numbers associated with their BINs are found. Financial institutions have used the alerts to create automated and tailored actions, including automatically disabling cards or notifying customers.
Blog
Strengthen Fiserv’s card fraud defense with Enzoic BIN Monitoring—real-time dark web alerts that help stop fraud before it starts.
Blog
63% of US cardholders have fallen victim to fraud. One critical area of risk is the exposure of full payment card numbers on the dark web.
Blog
A deep dive into some real-live techniques and scripts used by threat actors to commit credit card fraud. See the actual steps involved.
Harnessing Dark Web intelligence to prevent attacks associated with compromised credit and debit cards.
Contact Us