A series of simple, hosted REST APIs connected to our massive database of compromised credentials and accounts for integration into your application or website.
Try Now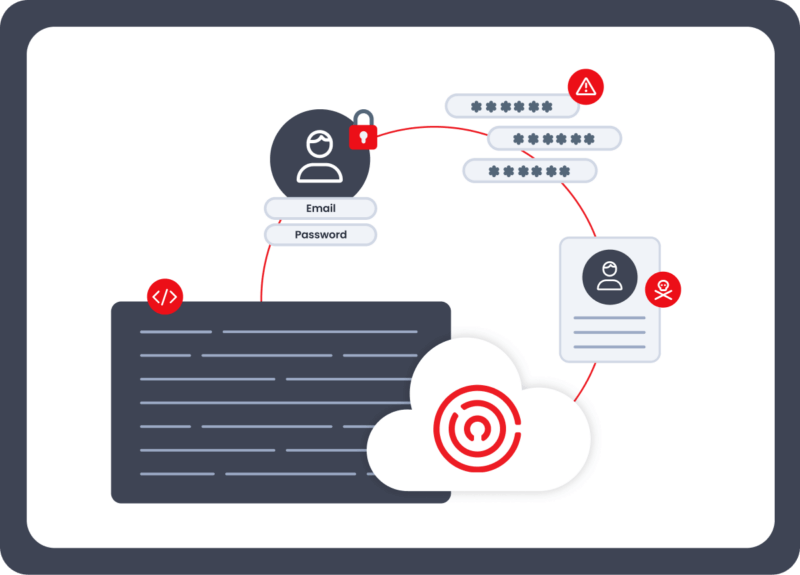
HOW IT WORKS
Enzoic’s APIs make it straightforward to check for exposed passwords, compromised credentials, and identity or PII breach indicators. Call our REST endpoints directly or use our SDKs for fast integration into authentication, IAM, fraud, and security workflows.
An exposure is any unintended release of user credentials. This could be due to a data breach at a site, malware that has captured user credentials, a phishing site collecting passwords, or other unauthorized leaks.
Look up all the exposures for your users and obtain detailed information about each.
A compromised password is any password that has been found in a data breach, cracking dictionary, or underground password list used by cybercriminals.
Check whether a password is unsafe before allowing a user to create or update it.
A compromised credential is an exact username and password combination found in a data breach, data exposure, or combo list used by attackers.
Determine whether a username/password combination is available to hackers.
A credential breach occurs when an email address or domain appears in newly discovered breach data, credential leaks, or infostealer logs on the dark web. This may include large-scale data breaches, targeted malware infections, or credential dumps.
Receive real-time alerts when monitored emails or domains show up in a new breach so you can notify users, increase authentication requirements, or trigger secure resets automatically.
An identity breach happens when sensitive personal attributes—such as names, email addresses, phone numbers, login identifiers, or financial and account data—appear in breach data or dark web sources. This can lead to targeted fraud, impersonation, or account takeover.
Register full identities to receive alerts when high-risk or high-value identity attributes are detected in new breaches or underground datasets.
HOW IT CAN HELP ME
Enzoic’s APIs are built for reliable, low-friction integration into authentication, identity, fraud, and security workflows. Whether checking passwords during account creation or monitoring users and domains for new breach activity, the APIs help teams respond quickly and reduce exposure risk.
![]()
Get started with a free API key for password, credential, and exposure checks. Our usage-based plans scale from small projects to high-volume production workloads, with additional services like breach and identity monitoring available as your needs grow.
All APIs are callable directly via REST, but the fastest integration path is through our language-specific SDKs. Each API includes copy-and-paste examples, Quick Start tutorials, and code samples to help you implement password screening or breach monitoring in minutes.
Our APIs provide multiple ways to reduce risk—blocking unsafe passwords, detecting compromised credentials, and monitoring users or domains for new breach activity. This helps teams remediate early and prevent damage before attackers can exploit exposed data.
Enzoic’s APIs are designed for fast, reliable integration into authentication, IAM, fraud, and security workflows. The flexible architecture makes it easy to embed credential checks or breach monitoring into existing systems or new applications.
KEY BENEFITS
Enzoic’s real-time breach and credential intelligence provides measurable security improvements across password, credential, and identity workflows. These APIs help teams reduce risk and act earlier when user data appears in new breaches.
Identify compromised credentials before attackers can use them during login attempts.
Add real-time risk signals to password creation, reset flows, and ongoing identity verification.
Monitor emails, domains, and identity attributes for new breach activity so you can respond quickly.
Enrich existing systems with high-quality breach and credential intelligence to reduce risk without adding friction.
Align with NIST SP 800-63B guidance through continuous password and credential checks.
Trigger alerts, step-up authentication, or password resets automatically when new exposures are detected.

Explore API references, Quick Start guides, SDKs, and code snippets that show exactly how to integrate password screening, credential checks, or breach monitoring into your workflows.
Read API DocsAt Enzoic, security and privacy are foundational to everything we build. Our services are architected to give you powerful protection—without exposing your users’ sensitive data.
Enzoic’s APIs run entirely in the cloud on Amazon Web Services (AWS) using a multi-layered architecture designed for high security and resilience.
All traffic to and from our APIs is encrypted using HTTPS and TLS 1.2, with 256-bit encryption to keep data safe in transit.
We never store or log passwords or credential hashes that you submit to the Passwords, Credentials, or Exposures APIs. Those checks use a privacy‑preserving, partial‑hash method.
Queries sent to our Password, Credential, and Exposure APIs are processed in memory only. We do not write or retain any submitted data, ensuring no risk of long-term exposure.
When monitoring for exposure, we store only encrypted, hashed values of credentials in a secure database. Sensitive customer data is encrypted both at rest and in motion.
These practices allow organizations to confidently use Enzoic without introducing new data handling risks or compromising user privacy.
Enzoic never ingests or stores full passwords—offering a privacy-first alternative to legacy vendors.
Tim Nufire, Founder & Chief Cloud Officer
“We’re impressed with Enzoic’s creative approach to catching credential stuffing attacks using their database of compromised credentials as a proactive defensive against ATO. Enzoic does this securely without cracking hashed passwords or being given access to our users’ credentials and doesn’t add unnecessary steps to our customers’ login process.”
Calls
Free for up to 2,000 Calls!
First 2,000 Calls: $0 / Call Next 3,000 Calls: $0.040 / Call Next 5,000 Calls: $0.020 / Call Next 40,000 Calls: $0.015 / Call Next 50,000 Calls: $0.010 / Call Next 100,000 Calls: $0.008 / Call Next 800,000 Calls: $0.005 / Call Over 1M Calls: Contact Us
Contact Us
Billing Cycle
-
Monthly
Custom
Payment Methods
-
Credit Card
Custom
Max Calls
2,000
1,000,000
Custom
Support
Self-Service / Knowledge Base
24-hour response during business week
4-hour response during business week
SLA
-
-
Custom
Passwords API
Credentials API
Exposures API
Cleartext Credentials API
-
-
Blog
Attackers can use compromised credentials to gain unauthorized access to an organization's information, leading to ATO attacks.
Blog
Ensure GDPR Compliance and Protect Your Organization from Costly Penalties. Learn the key steps to take when handling EU citizens' data in the event of a data breach.
Blog
Credential stuffing attacks are posing major risks to banks and credit unions. Read how to address the vulnerabilities in open banking.
Start building with simple, secure tools for password, credential, and breach monitoring.
Experience Enzoic