For many cybersecurity professionals, one of the more surprising ideas to come out of 2019 is the recommendation to drop forced password expiration policies. Forced password expiration policies have been around for many years now and are a widespread element of cybersecurity frameworks within organizations across the world over. However, we’re now being told they may not be necessary. Password expiration policies have been recommended for decades, what changed?
Put simply, for a cybersecurity policy to be considered fit, it has to have the following properties:
The industry has now had many years to analyze both the cybersecurity effectiveness and the cost-effectiveness of forced periodic password resets, and it turns out they are falling short on both of these objectives.
In 2019, Microsoft dropped the forced periodic password change policy in their security configuration baseline settings for Windows 10 and Windows Server, calling them obsolete mitigation of very low value. Microsoft claims that password expiration requirements do more harm than good because they make users select predictable passwords, composed of sequential words and numbers, which are closely related to each other. Additionally, Microsoft claims that password expiration requirements limit containment because cybercriminals almost always use credentials as soon as they compromise them. The US-Based National Institute of Standards and Technology outlined in NIST 800-63b also updated the NIST password guidelines to reflect the same sentiment; that passwords shouldn’t periodically expire.
Both NIST and Microsoft are highly influential in the cybersecurity guidelines landscape. NIST provides guidelines primarily for US federal agencies, but their guidelines are used by private companies globally. The idea here is that if the NIST password guidelines are good enough for US federal agencies that deal with some of the most sensitive data in the world, then they’re good enough for most organizations. Similarly, Microsoft has significant sway in the private sector due to its long-standing success and market presence with Active Directory. When two major organizations of this scale decide to drop a traditional cybersecurity practice, it is not without good reason. Multitudes of small, medium and large organizations are going to follow suit. Let’s delve into why forced password expiration policies are no longer needed.
Most users are familiar with password rotation policies. While different companies have different practices when it comes to forced periodic password resets, it’s typical for companies to force users to change their password every 30, 60, or 90 days.
In fact, according to a Forrester Research study, 77% of IT departments expire passwords for all staff quarterly. Although many users find these forced password resets frustrating, they did make sense when the computing landscape was more straightforward for the average employee. The password expiration policy made sense in a time where employees would typically only have one or a few passwords to remember. Learning one new password, even every 30 days, is not a difficult task when you only need one password.
However, as our workplace and technology has progressed, most employees now find themselves needing to remember multiple passwords for all of their accounts. More complexity is added when each of these individual accounts has its own password expiration policy. Further complicating this issue is that most people have personal and work online accounts.
A joint study conducted by Mastercard and the University of Oxford found that “21% percent of users forget passwords after 2 weeks, and 25% forget one password at least once a day.” This particular study is focused on password use for e-commerce sites, and how passwords have a detrimental effect on sales, however, the point still stands. Users in the digital age have far too many passwords to remember, and we’re failing at remembering them. And what happens when an employee can’t remember their password? They often have to reset it using the IT Help Desk at work.
It costs IT departments large amounts of money to fund these password resets for Active Directory accounts. Forrester cites that it costs $70 of IT Help Desk labor for a single password reset. When you consider that 20% to 50% of all Help Desk calls are for password resets, it’s easy to see how password resets can get expensive quickly.
Lost time is also a significant factor in why password resets are so expensive for companies. A survey by Onelogin found that an organization spends an average of 2.5 months a year on password resets alone. The actual figure may even be higher than this due to 24% of respondents not knowing how much time was spent on password resets. The costs aren’t just accrued from the time spent by the IT Help Desk, but also from the lost productivity of the employees who have forgotten their password. A new password study by HYPR found that 78% of people had to reset a password they forgot in the past 90 days.
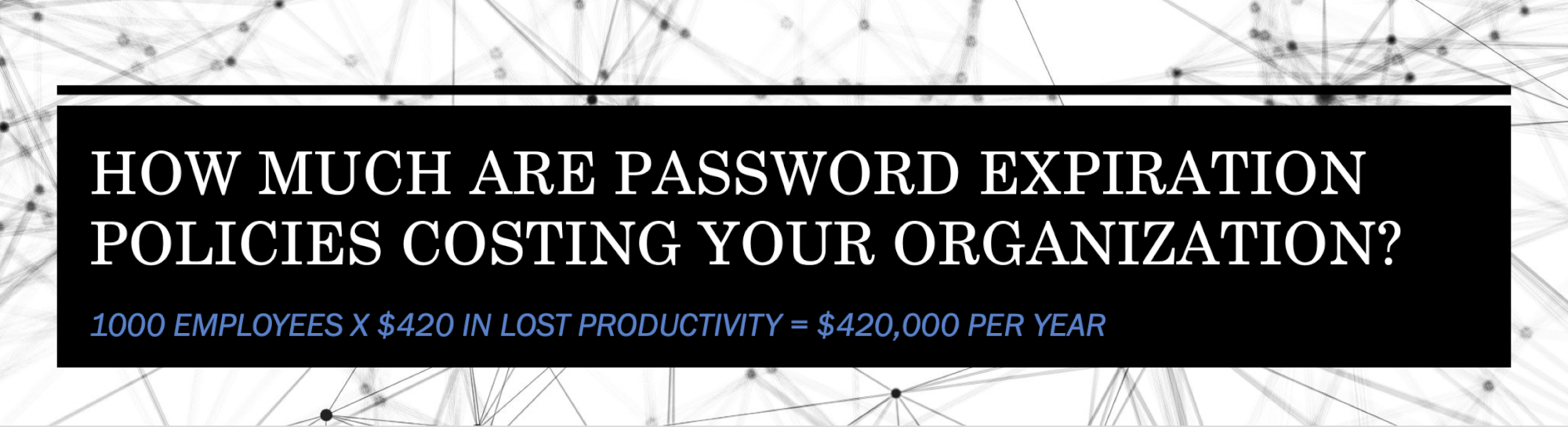
All of this time lost to password resets is estimated to cost companies $420 per employee in lost productivity per year, according to a study by Widmeyer and sponsored by Centrify Corporation. If you scale this up to an enterprise with 500 employees, according to this study, the loss is equivalent to nearly $210,000 per year in productivity.
The primary purpose of a password policy is to protect company systems and data from bad actors with nefarious intentions. However, a password policy will struggle to do this if users struggle to follow the policy. This is one area where forced password rotation fail companies.
As we discussed above, users now have far too many passwords to remember. Too many passwords lead to something called password fatigue. People feel frustrated at the excessive amount of passwords they need to remember as part of their daily routine and the requirements around these passwords. The leading causes of password fatigue are:
When users become fatigued with having to remember excessive passwords, they take steps to make the process easier. This usually means creating new passwords that are slight variants of their original password or creating weak passwords that are easy to remember. Weak passwords are a severe threat to an organization’s security and can potentially cost the company vast amounts of money in the form of a data breach. According to Verizon’s Data Breach Investigations Report, over 70% of employees reuse passwords at work.
Forced periodic password resets can encourage poor password hygiene, which puts companies at even higher risk of a costly data breach.
Kristen Ranta Haikal Wilson, Cofounder, CMO, & Product, Enzoic
Don’t users know better than to reuse passwords? After all, recommendations against reusing passwords have been around for over a decade now. Well, yes, they do understand. According to the same study, 91% of respondents said they knew reusing passwords is poor practice, but 59% said they reuse their passwords everywhere (both at home and at work). The global average total cost of a data breach in 2019 is $3.92 million. It’s even bleaker in the US, where on average, a data breach costs a company $8.9 million.
So, if password expiration policies are no longer effective, then what is? What should replace it? The current recommendation is that after creation, passwords should be checked against a continually updated list of exposed passwords.
The list of compromised passwords would be screened against Active Directory passwords daily. A user’s password should be screened daily after it has been created and accepted. This regular screening is vital because a password may be perfectly safe when it is created, but it can quickly become exposed in a data breach or leak at a later date without the user’s knowledge.
Users benefit from this system because they don’t have to continually create and remember new passwords, which should free them up to choose a more secure password. If a user’s password does become compromised, they will be notified that their password is insecure and can be prompted to change it now or at a later point. The theory now is that unless an employee’s password is found to be compromised or in a cracking dictionary, they shouldn’t have to change their password. The company benefits from increased security due to more secure user passwords, and with dramatically fewer password resets, the IT Help Desk costs decrease considerably.
Forced periodic password resets are no longer necessary in a modern world with nuanced cybersecurity requirements. It is now clear that not only do password resets carry a high cost, both in terms of Help Desk costs and lost productivity, but they also encourage poor password practices. A better solution now exists in the form of compromised password screening tools that increase security, reduce friction for employees, and reduce costs for the company.
Learn more about Automated Password Monitoring and NIST Password Guidelines in Active Directory.