Exposed credentials continue to be a leading cause of data breaches, making it a top priority for organizations to protect themselves from this threat. Active Directory is particularly appealing to attackers; infiltrating just one account can grant them access to a company’s critical data and infrastructure. Alarmingly, threat actors on the Dark Web traffic a staggering number of compromised credentials, a substantial chunk of which could be active in domains you oversee. This presents both a duty and an opportunity for security professionals — whether they are Managed Service Providers (MSPs), tech resellers, working in-house, or representing other important stakeholders — to aid their organizations and clients in planning effective strategies to guard against the risk of credential compromise in Active Directory.
Enzoic for Active Directory is a foundational tool for those looking to strengthen their defenses against credential-based attacks. This robust solution goes beyond simple scans, offering continuous protection and automated remediation to ensure your Active Directory environment remains secure.
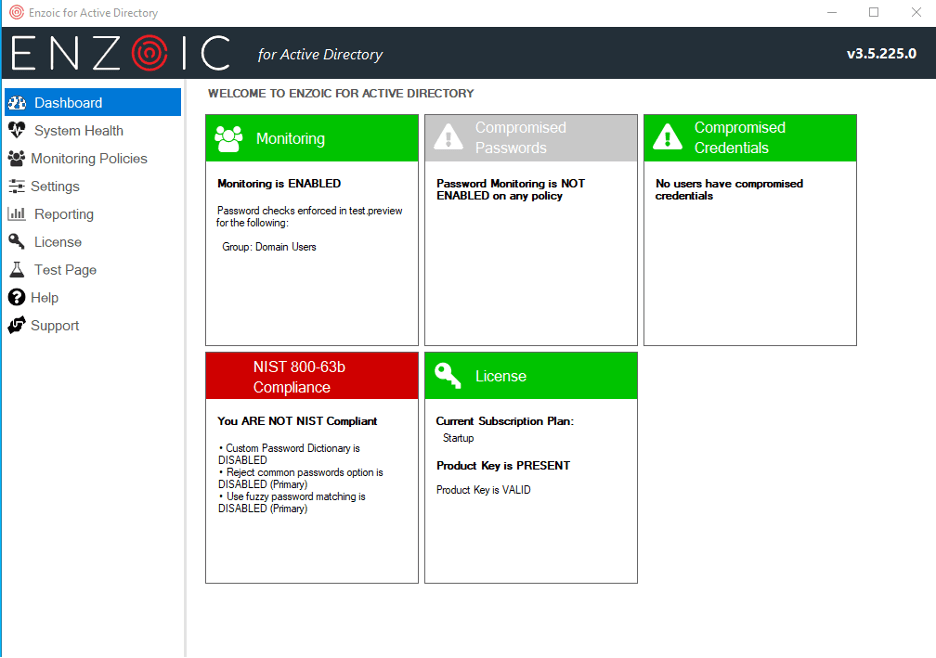
Enzoic for Active Directory is designed for seamless integration and continuous protection. It’s a powerful resource for MSPs, MSSPs, and resellers who are responsible for advising clients and protecting multiple environments. Here’s why the full Enzoic for Active Directory solution is the optimal choice:
For Managed Service Providers (MSPs), MSSPs, and resellers, offering a solution like Enzoic for Active Directory not only enhances security but also demonstrates a commitment to providing top-tier protection for your clients. Here’s how it benefits you:
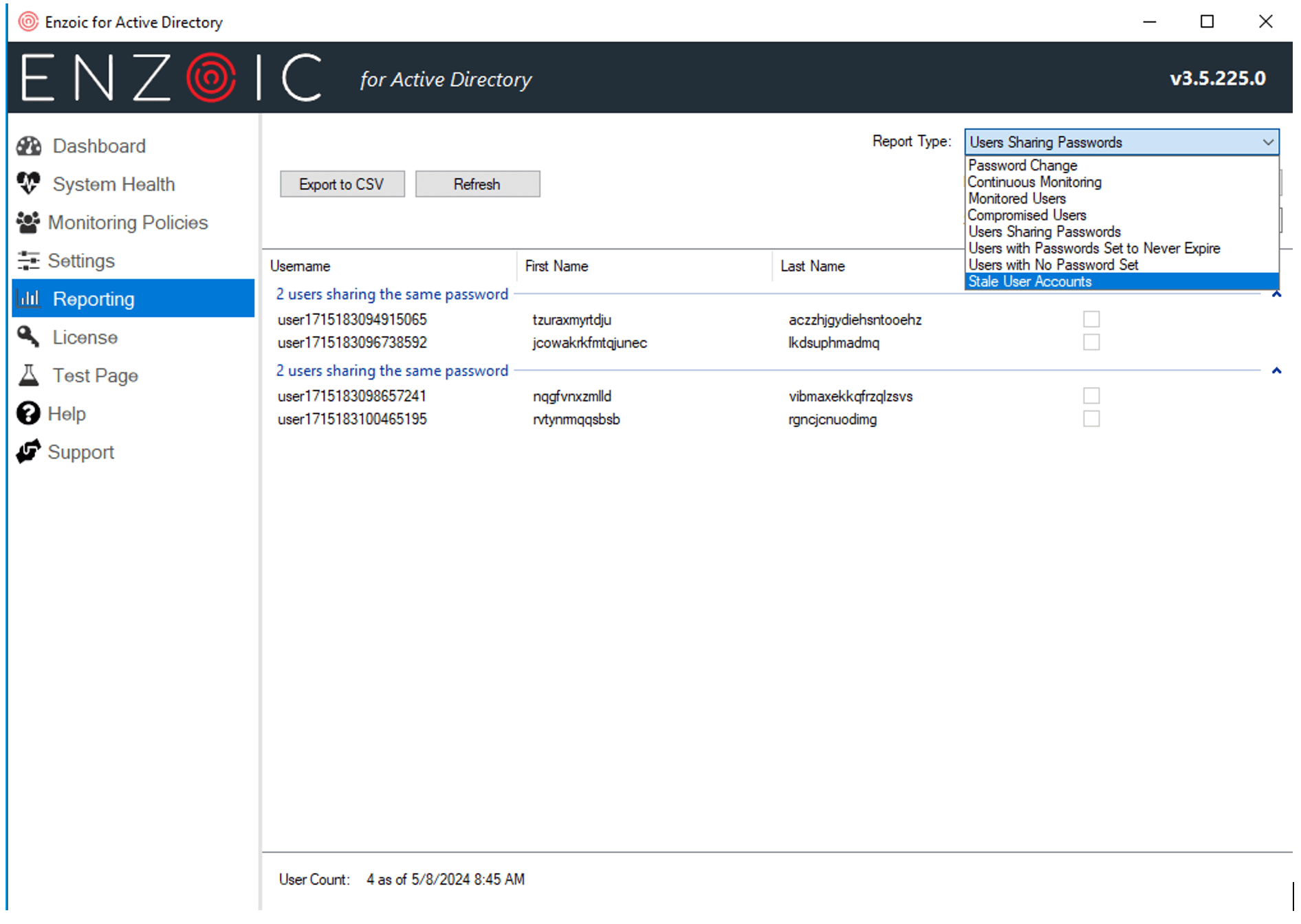
Don’t let compromised credentials be the weak link in your customers’ security chain. Enzoic for Active Directory provides a comprehensive, automated, and continuous security solution tailored for modern IT environments. You can try Enzoic for Active Directory free for up to 20 users. Elevate your security posture and protect your clients with the full Enzoic for Active Directory solution.
You can also get a snapshot of an environment’s risk with our free password audit tool. Experience how it can transform your security approach with seamless integration and robust protection. Enhance security, reduce costs, and provide peace of mind to your clients with Enzoic.
Contact us today to learn more and get started with Enzoic for Active Directory.
AUTHOR
 Josh Parsons
Josh Parsons
Josh is the Product Marketing Manager at Enzoic, where he leads the development and execution of strategies to bring innovative threat intelligence solutions to market. Outside of work, he can be found at the nearest bookstore or exploring the city’s local coffee scene.
Explore free for up to 20 users. Save hours of admin time and simply get started with a password monitoring solution.