A Multi-Layered Defense for Password Security
Using Duo Security for multi-factor authentication (MFA) is a smart way to protect logins, but even with MFA in place, weak or compromised passwords remain a serious risk. That’s where Enzoic for Active Directory comes in. Enzoic adds an extra layer of password security by actively screening and monitoring passwords against real-time breach data. Integrating Enzoic with Duo gives you the best of both worlds: strong MFA from Duo, and continuous compromised-password protection from Enzoic, resulting in a cohesive, multi-layered defense. In this post, we explain why this integration is valuable and walk through how to implement the Enzoic + Duo integration in a few simple steps.
Elevated Credential Security: By combining Enzoic with Duo’s MFA, organizations significantly improve credential safety. Enzoic continuously monitors passwords for compromise and automatically enforces changes when a password becomes unsafe. Meanwhile, Duo ensures every login is verified with a second factor. Together, they address both something you know (password security) and something you have (MFA), dramatically reducing the risk of breaches.
Address Password Weaknesses MFA Doesn’t Cover: Duo may require a second factor, but it doesn’t check if the password itself is weak or known to attackers. Many breaches still originate from compromised or common passwords – in fact, 81% of hacking-related breaches involve stolen or weak passwords. Enzoic fills this gap by enforcing modern password policies: it screens new passwords against billions of known compromised credentials and common password patterns, per NIST guidelines. This ensures users aren’t using passwords that attackers could easily guess or that have appeared in breach databases.
Seamless, Conflict-Free Integration: If you already use Duo (or plan to), adding Enzoic is straightforward and won’t interfere with your existing MFA workflow. Enzoic’s client is designed to wrap around Duo’s credential provider on Windows, rather than conflict with it. The configuration involves minimal steps (essentially just exchanging each product’s GUID as explained below) and ensures both tools work in harmony. There’s no need to disable anything in Duo or vice-versa – they operate side by side without user friction. In short, Enzoic integrates easily with Duo with no conflicts and very little configuration effort.
When integrated with Duo, Enzoic for Active Directory provides critical protections at each stage of the password lifecycle:
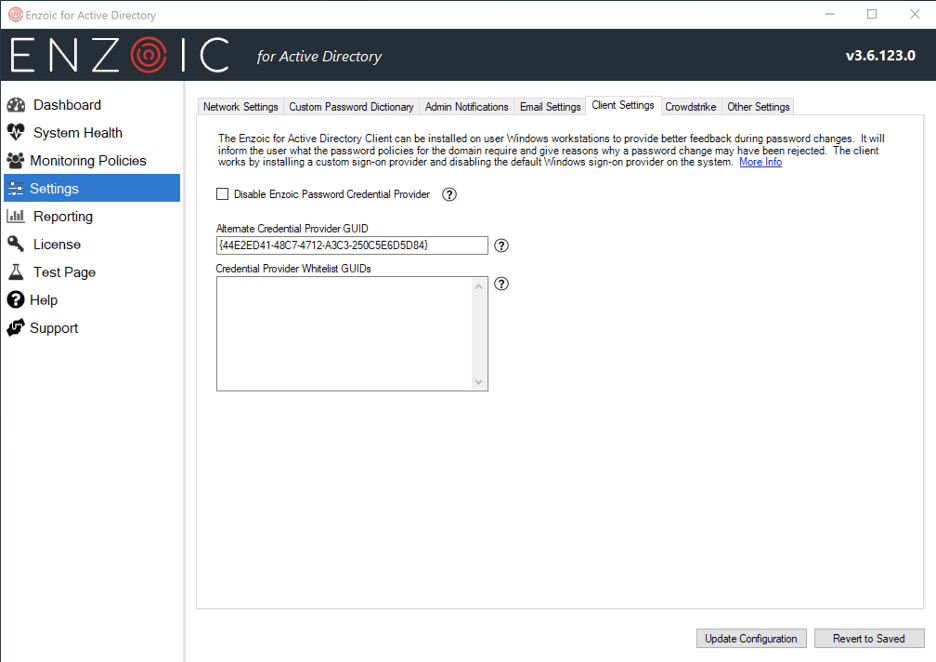
Setting up Enzoic to work alongside Duo is straightforward. Essentially, you need to let each product know about the other’s credential provider so they can function together. Here’s how to implement the integration step-by-step:
View the full integration guide in Enzoic’s support documentation here
For end-users, the login and password update experience remains straightforward and familiar:
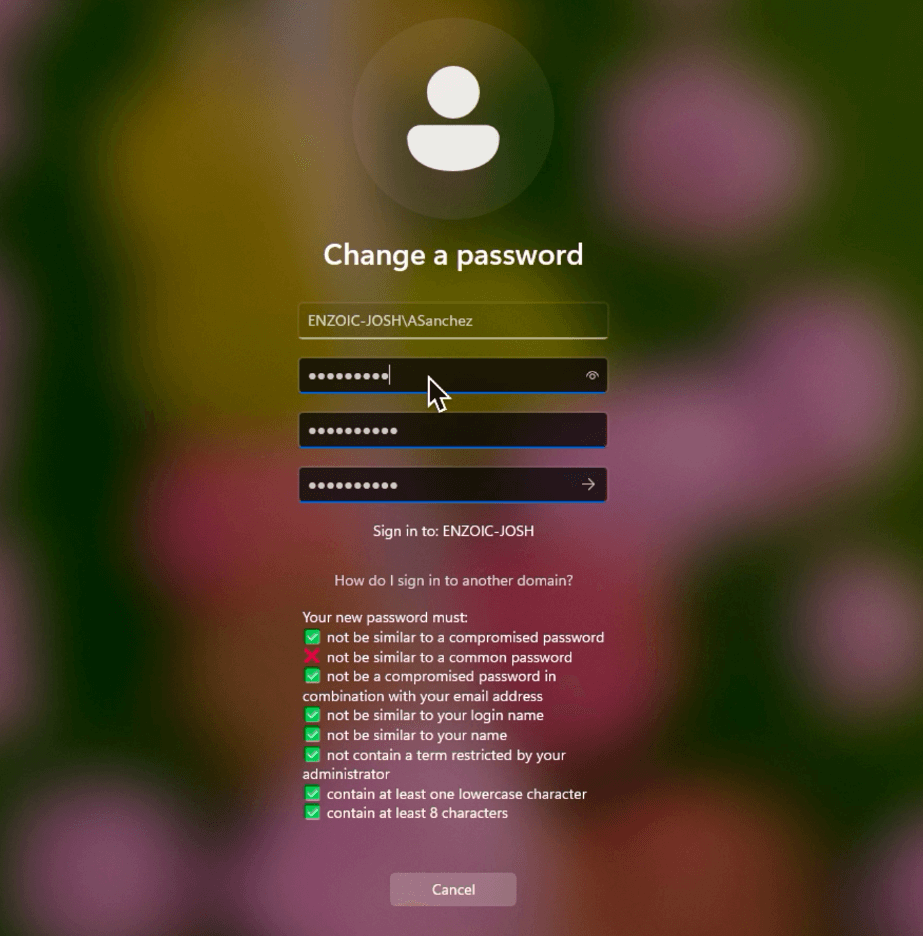
This integrated flow ensures that users are prevented from using risky passwords but are not burdened with any new steps during login. If their password ever becomes compromised down the line, Enzoic can force a change (which the user will experience as a prompt to update their password at next login), but after that they continue with Duo MFA as usual. From the end-user perspective, security is tighter without making their login process more complicated. Your first factor, the password, is now your strongest defense.
Implementing Enzoic alongside Duo is a simple yet highly effective way to strengthen your organization’s defenses. With minimal configuration, you gain continuous password compromise monitoring on top of strong MFA – covering two critical aspects of account security without any usability sacrifice. Enzoic + Duo work in tandem to stop weak or breached passwords from creeping into your systems and to block unauthorized access even if credentials are stolen. The integration is quick to set up (often just a few minutes) and supported by both vendors’ documentation, with no additional licensing cost if you already use Enzoic for Active Directory and Duo. Don’t leave the password half of the authentication equation vulnerable, strengthen it with Enzoic, and let Duo handle the rest. Your users will likely never know the difference, but your security team certainly will.
AUTHOR
 Josh Parsons
Josh Parsons
Josh is the Product Manager at Enzoic, where he leads the development and execution of strategies to bring innovative threat intelligence solutions to market. Outside of work, he can be found at the nearest bookstore or exploring the city’s local coffee scene.
We make it easy to try, implement and protect. Start building for free.